National Cyber Director Sean Cairncross is leading a White House initiative to systematically identify security vulnerabilities across America’s critical infrastructure—specifically the attack surfaces that AI systems can exploit—according to a Wall Street Journal report published April 12, 2026. The program represents the first formal federal effort to assess infrastructure risk through an AI-threat lens, arriving as adversarial nation-states accelerate their deployment of machine learning tools against US systems.
This is not preparedness theater. The premise—that AI fundamentally changes the vulnerability calculus for critical infrastructure—is correct, and formalizing it now is overdue.
What AI-Exploitable Actually Means
Traditional infrastructure attacks require skilled human operators to map networks, probe configurations, and develop exploits—a process measured in weeks. AI compresses that timeline to hours. Automated systems can scan thousands of industrial control system endpoints simultaneously, correlate network traffic patterns to identify exploitable timing windows, and adapt attack strategies in real time based on defensive responses.
The shift is qualitative, not just quantitative. An AI-assisted attacker probing a water treatment plant’s SCADA system can test thousands of undocumented command variants in the time a human analyst would spend configuring their toolkit. A substation running 30-year-old firmware becomes a different class of target when adversaries can enumerate its weaknesses at machine speed—without fatigue, without diminishing returns.
The Sean Cairncross AI cyber initiative targets this specific gap: cataloging which systems and configurations become materially more dangerous when adversaries operate with AI assistance—a narrower, more actionable frame than generic vulnerability assessments.
The Power Grid Gets First Attention
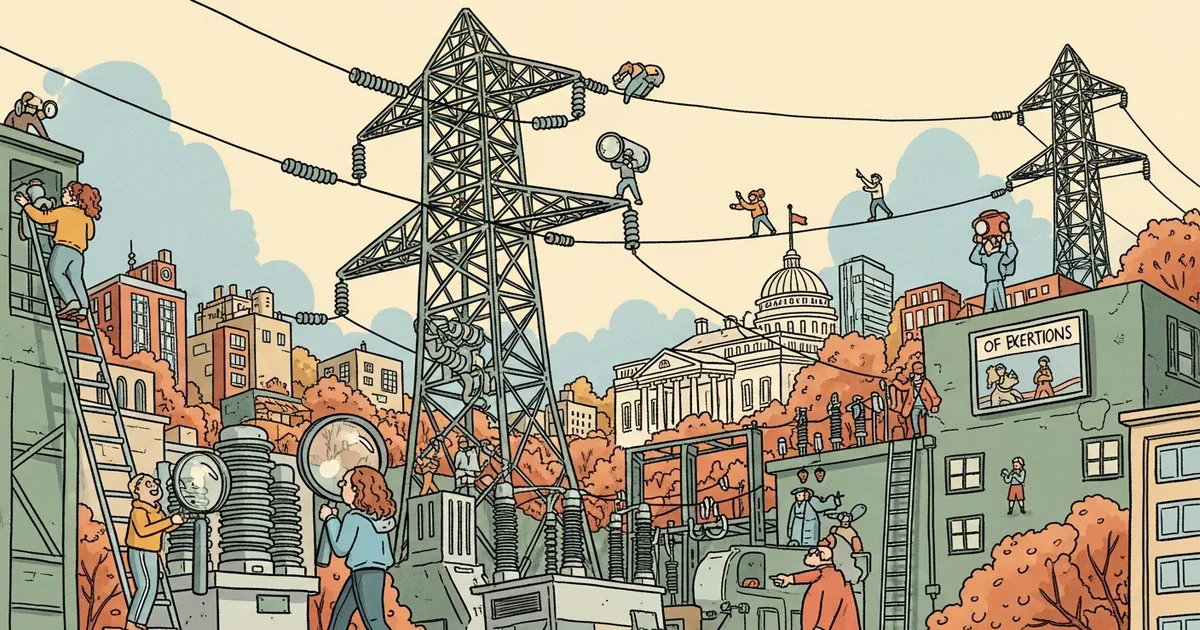
America’s electrical grid runs on infrastructure built before internet connectivity was a design consideration. More than 55,000 substations operate supervisory control and data acquisition (SCADA) systems—many from the 1990s—that were gradually networked for remote monitoring without proportional security investment. The result is a massive, heterogeneous attack surface with deeply uneven defensive posture across thousands of independent operators.
The IT/OT convergence problem is structural. Operational technology systems were engineered for reliability and longevity, not for internet-connected threat models. Industrial control system vulnerabilities have grown for five consecutive years, per Dragos’s annual OT cybersecurity reports. AI makes probing those systems at scale feasible for adversaries who previously lacked the human operator capacity to target them systematically.
Energy and water infrastructure get priority for a direct reason: disruption is immediately life-threatening. A compromised financial system causes economic damage. A compromised power grid in winter causes deaths.
The Threat Actors Are Already Inside
Volt Typhoon, a Chinese state-sponsored hacking group, was attributed by CISA, the NSA, and the FBI in February 2024 as having spent at least five years pre-positioning inside US critical infrastructure. The operation was not espionage—it was strategic positioning to enable service disruption during a future conflict. Targeted sectors included power utilities, water systems, ports, and telecommunications.
Salt Typhoon separately compromised at least nine major US telecommunications carriers in 2024, gaining persistent access to call records and metadata for millions of Americans. Both operations represent patient, methodical infrastructure mapping at a scale that AI-assisted tools would have achieved in a fraction of the time—which is precisely the risk Cairncross is now mapping.
Russia’s Sandworm group executed what security researchers consider the first AI-assisted attack on power infrastructure, targeting Ukraine’s grid in 2016 with automated sequences designed to maximize disruption. That template has been iterated and is accessible to any state actor with resources and motivation. The US grid is a larger, more complex version of the same target class.
Cairncross’s Structural Problem
Sean Cairncross was confirmed as National Cyber Director in March 2025, inheriting an office that has struggled since its 2021 creation to define its mandate among competing federal entities—NSC, CISA, NSA, and CYBERCOM each hold overlapping cybersecurity authorities. The current initiative reportedly involves cross-agency coordination to produce a structured, prioritized vulnerability catalog, not merely another threat intelligence report.
The scope covers all 16 critical infrastructure sectors defined by the DHS framework. Getting accurate vulnerability data requires private-sector cooperation—utilities, water authorities, and pipeline operators own the majority of US critical infrastructure—and that cooperation has historically been inconsistent, shaped more by liability concerns than security incentives.
Congress has not passed critical infrastructure security mandates with real enforcement mechanisms. Without legislative authority to compel remediation, the best-case outcome for this catalog is a classified briefing that motivates action. The worst case: a detailed vulnerability inventory that, if leaked, functions as an attack playbook. The NSA’s EternalBlue exploit was stolen and ultimately powered the WannaCry ransomware attack that disrupted hospitals across 150 countries in 2017—a precedent this initiative cannot ignore.
The Remediation Gap Is the Real Problem
Cataloging vulnerabilities is considerably easier than fixing them. Power grid operators cannot patch a SCADA system mid-operation. Water treatment plants run on equipment with 20-to-40-year lifecycles. Financial institutions have regulatory change-management processes that make rapid patching difficult. Each sector has structural reasons why known vulnerabilities persist for years after discovery.
The recent Anthropic source code exposure demonstrated that even organizations built around security engineering operate with exploitable gaps. Critical infrastructure operators are, in most cases, running older systems with smaller security budgets. The window between “identified vulnerability” and “patched vulnerability” is exactly where attacks live—and AI makes that window more dangerous, not shorter.
MegaOne AI tracks 139+ AI tools across 17 categories, and AI-assisted penetration testing and OT vulnerability discovery tools are among the fastest-growing segments in 2026. Offensive capabilities are democratizing faster than defensive infrastructure is being hardened.
The Dual-Use Problem Nobody Wants to Address
The methodology Cairncross’s team develops to find AI-exploitable vulnerabilities is, structurally, an offensive tool. Any systematic approach to mapping these weaknesses constitutes a template that—if leaked—becomes an attack playbook. This is not a theoretical risk; it is the EternalBlue failure mode reproduced at infrastructure scale.
This is not an argument against the initiative. It is an argument for classifying the assessment at the level of a weapons program—with compartmentalization and access controls proportional to the damage it would cause in adversary hands.
The geopolitical dimension compounds urgency. As AI infrastructure scales globally—with companies like Nebius developing $10 billion data centers near strategically sensitive borders—the physical and digital infrastructure of AI capability has itself become a target class. Critical infrastructure security and AI infrastructure security are increasingly inseparable conversations.
The broader public concern is real. The Humans First movement’s anxieties about AI operating beyond human oversight speak directly to this moment: Cairncross’s initiative is, in part, a formal assertion that human analysts will understand what AI can do to the grid before adversaries demonstrate it operationally.
Two Tests This Initiative Must Pass
The White House is correct that AI creates a qualitatively new infrastructure threat model. Treating it as an incremental upgrade to existing cyber risk—rather than as a force multiplier that changes which vulnerabilities are exploitable and at what speed—was the wrong frame. The correction is overdue.
Whether this produces actual security improvements depends on two things: whether findings can be translated into remediation mandates with enforcement authority, and whether the assessment itself can be secured against the kind of exposure that converts a defense asset into an attack resource.
Critical infrastructure operators should not wait for the federal catalog. AI-assisted OT security assessments are available now from vendors including Claroty, Dragos, and Tenable OT. Running them before the government publishes its findings is the minimum viable posture for a sector that Volt Typhoon has already proven is being systematically mapped by adversaries operating at machine speed.