- Anthropic accidentally exposed 513,000 lines of Claude Code source via an npm packaging error on March 31, 2026.
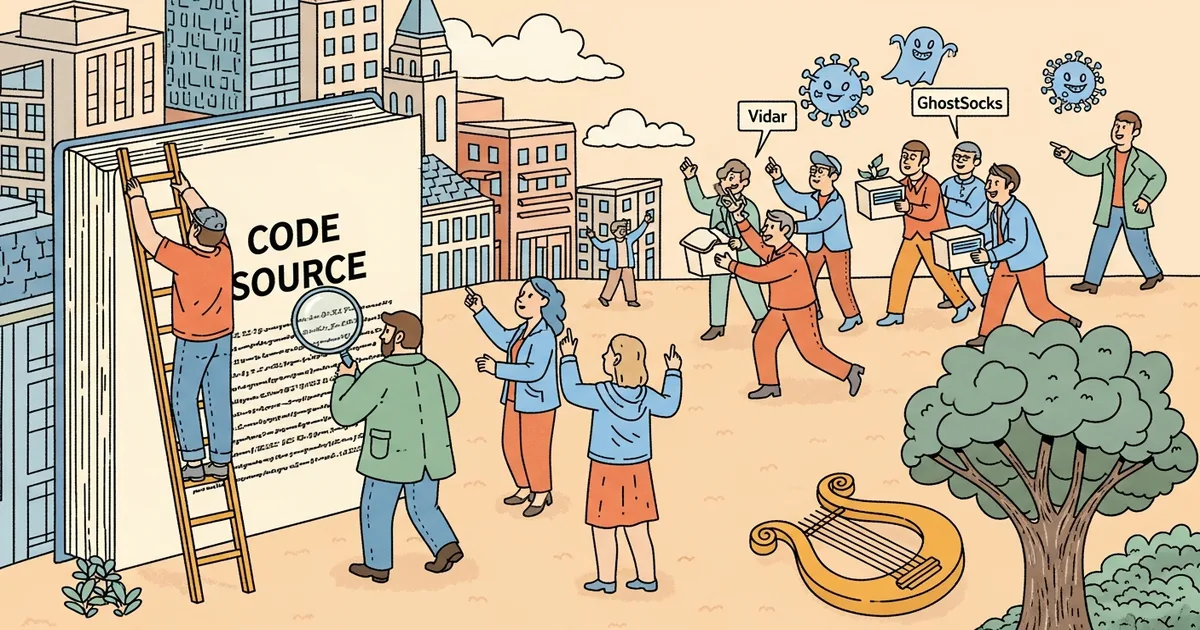
- Malicious GitHub repositories claiming “unlocked enterprise features” appeared within 48 hours, distributing Vidar v18.7 infostealer and GhostSocks proxy malware.
- A trojanized npm package was available for approximately 3 hours, potentially affecting users who installed or updated during that window.
- Attackers also staged dependency confusion attacks by typosquatting internal npm package names referenced in the leaked code.
What Happened
Hackers are exploiting Anthropic’s accidental source code leak of Claude Code to distribute malware through fake GitHub repositories and trojanized npm packages. On March 31, 2026, a 59.8 MB JavaScript source map containing 1,906 unobfuscated TypeScript files was inadvertently included in a published npm package. The exposed code contained orchestration logic, permissions systems, execution internals, and hidden features. Within 48 hours, threat actors created SEO-optimized GitHub repositories claiming to offer unrestricted versions of Claude Code.
Why It Matters
The incident combines two attack vectors: a supply chain compromise through npm and social engineering through fake repositories. Security firm Zscaler identified at least two malicious repositories, one by a user “idbzoomh,” that appeared among the first Google search results for “leaked Claude Code.” Legitimate repositories containing the leaked source were forked thousands of times, creating a large attack surface for distributing modified versions with embedded payloads.
Technical Details
The malicious repositories deliver malware via 7-Zip archives containing a Rust-based executable named ClaudeCode_x64.exe. The archives were updated frequently with potential payload variations. Two malware families have been identified: Vidar v18.7, an infostealer that collects account credentials, credit card data, and browser history; and GhostSocks, which turns infected devices into proxy infrastructure that criminals use to mask their network location.
Separately, users who installed or updated Claude Code via npm on March 31 between 00:21 and 03:29 UTC may have pulled a trojanized version containing a cross-platform remote access trojan. Attackers also exploited internal package names visible in the leaked source to stage dependency confusion attacks through typosquatted npm packages.
Who’s Affected
Developers who downloaded Claude Code from unofficial sources or updated via npm during the 3-hour exposure window face the highest risk. The Vidar infostealer targets saved credentials and financial data stored in browsers, making any developer with saved GitHub tokens, cloud API keys, or payment information in their browser a potential victim. Organizations with developers using Claude Code should audit npm installation logs from March 31.
What’s Next
Anthropic has removed the exposed source map from subsequent npm releases. GitHub has been notified about the malicious repositories, though the SEO manipulation means new ones may continue to appear. Developers should verify their Claude Code installations against official checksums and rotate any credentials that may have been stored in browsers on affected machines.